The cloud. It’s become as ubiquitous as the air we breathe. Millions of businesses rely on it to store and access data, facilitate communication, and run essential applications. However, it’s this vast dependence that paints a colossal target on its back. In the wake of several high-profile security breaches, it begs the question: Are we ready for the next big cloud breach?

The Alarming Reality of Cloud Security
To truly prepare for a cloud breach, we must first understand the nature of the beast we’re dealing with. As the adage goes, “know thy enemy.” Security threats in the cloud can originate from a myriad of sources – from misconfigured settings to sophisticated cyber-attacks. And the ramifications can be dire: interrupted business operations, damaged reputation, and significant financial loss.
A crucial part of grappling with this reality lies in recognizing the role of open-source components in the software we utilize. They’re everywhere. In fact, open-source components constitute 60% to 80% of the codebase in modern applications.
This extensive use of open-source code brings with it increased exposure to potential vulnerabilities. It’s here that a process called software composition analysis (SCA tools) becomes instrumental. This procedure helps in identifying open-source components within a codebase, tracking their origins, and exposing any security vulnerabilities they may harbor. It’s like having a detailed map of your software’s DNA and knowing exactly where the weak points lie.
Armoring Up: Fortifying Your Cloud Defenses
So, how can we steel ourselves against the impending storm? As they say, the best defense is a good offense. Here are some proactive strategies to fortify your cloud defenses:
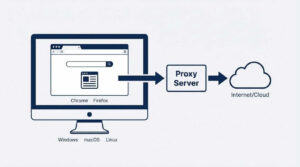
1. Implement Robust Security Measures: Leverage advanced security technologies such as firewalls, encryption, and intrusion detection systems. They form the first line of defense, a digital fortress against potential threats.
2. Regular Auditing: Regular security audits are like your periodic health check-ups – they help diagnose any underlying issues before they can escalate into more severe problems.
3. Educate Employees: Often, the weakest link in your security chain is human error. Regular training and awareness sessions can help employees identify threats and adhere to best security practices.
4. Data Backups: Always have a contingency plan. Regular data backups ensure that even in the face of a breach, you can quickly recover your data and resume operations.
5. Incident Response Plan: Prepare for the worst-case scenario. An effective incident response plan can help you respond quickly and decisively, minimizing the damage caused by a breach.
Embracing a Culture of Cybersecurity
Preparation doesn’t stop at implementing robust security measures. It’s about creating a culture of cybersecurity within the organization, where security is everyone’s responsibility. Employees need to be vigilant, always on the lookout for any signs of threats or breaches.
Furthermore, organizations must stay updated with the latest cybersecurity trends and threat intelligence. Just as hackers are always evolving their tactics, so too must our defenses adapt and grow stronger.
More on TechInDeep:
Predict, Prevent, and Pivot: Harnessing the Power of AI and Machine Learning
As we delve deeper into the age of artificial intelligence and machine learning, these technologies are proving themselves to be potent allies in our battle against cloud security threats. They can analyze enormous quantities of data, spot patterns, and predict potential breaches before they occur. Think of them as your digital crystal ball, giving you the power to foresee and prevent security incidents.
Moreover, machine learning algorithms can adapt and evolve in real-time, learning from new threats and enhancing your security systems’ effectiveness. It’s like having a cyber bodyguard that gets stronger and smarter with each passing day.
Building a Resilient Future
Ultimately, preparing for the next big cloud breach is an ongoing journey. It requires us to constantly evolve our strategies, innovate, and learn from our past mistakes.
The future is bound to bring more complex threats. However, with a robust security framework, the right technologies, and a culture of vigilance, we can not only be ready for the next big cloud breach but also ensure that our defenses are resilient enough to withstand it.
Remember, cybersecurity is a collective effort. We’re all in this together. Let’s learn, prepare, and stand strong. Because when the next big cloud breach hits – and it will – we’ll be ready. We’ll not only weather the storm, but we’ll emerge stronger and wiser, ready to take on the challenges of tomorrow.
Because in this ever-connected world, security is not just a need – it’s a responsibility. And we owe it to ourselves and to the generations to come, to create a secure, resilient digital landscape. So, let’s buckle up and get ready. The future awaits.







MAKECOMMENT