Table of Contents
How are VPNs Protecting the Smart Grids?
Virtual private networks are amazing tools for cybersecurity. Due to their capabilities and their effective performance against cyber threats, they are not only limited to PCs and Laptops anymore. Nowadays, you can use VPNs on just about any kind of device as long as it is connected to the internet.
To put the capabilities of the virtual private networks to the test, you can download Surfshark VPN and try it for yourself. However, for now, let’s keep this conversation focused on the role of VPNs in the cybersecurity of smart grids.
In this article, we will discuss how smart grids are vulnerable to different kinds of cyber threats and how a VPN can be helpful for their protection. So, without any further ado, let’s get started.

Cyber Threats to Smart Grids
The term ‘smart grid’ has been used by many experts in order to describe a new generation of power transmission systems that are going to replace current centralized ones. What makes these new systems so great?
They will provide us with a more reliable electricity supply, lower energy bills, improved safety standards, and a cleaner environment.
However, all those wonderful features can come at a price: Cyber-attacks. Most of them have been published online over the past few years. Some of the main types of cyber threats to the smart grid systems are as follows:
Denial Of Service (DoS)
Distributed Denial Of Service (DDoS) attacks can take down large networks when attacked. The most common DDoS attack against utilities and critical infrastructure is called Low Orbit Ion Cannon (LOIC).
It works by flooding a target network with millions of small packets. Each packet contains a specific request or instruction from an attacker.
By sending these instructions/requests, the attackers can overload the target network resources which leads to disruption of service. In the case of smart grids, such disruptions can lead to loss of electricity supply.
Affected devices include routers, switches, data centers, SCADA systems, etc. Furthermore, some of the popular targets of DoS attacks are DNS servers, web servers, mail servers, etc., thus affecting websites and email services.
To protect your data center from these attacks, you need to install stateful firewall rules.
Man in the Middle (MitM) Attacks
Smart grids rely heavily on the security of the information flow between the smart meters and the control center. These flows contain important data about our electricity consumption in real-time.
Therefore, if someone manages to intercept these data, he may gain knowledge of the exact location and the behavior of each household through outages and spikes in usage.
This gives him access to personal details like credit card numbers, bank account balances, etc. Besides, having access to this sensitive data allows hackers to sell it to other people who want to steal money or cause harm.
Phishing
This one probably sounds familiar since it is commonly used by hackers to scam their victims. Instead of attacking a company directly, they send emails containing malicious links, attachments, and phishing emails asking users to disclose passwords.
Furthermore, a similar technique known as spear-phishing is also very effective. It requires specially crafted emails to trick innocent employees into disclosing their username and password credentials. As long as the user clicks on the link or downloads the attachment, his system gets infected with malware.
Data Loss Attacks
If there’s any way for hackers to get hold of your data, they will try to do it. For example, if you store your payment card numbers on a website that is accessible to everyone, you should think twice before doing so.
Similarly, if your company relies on a third party for its IT services, make sure that they keep your data secure in order to avoid any breach of customer privacy. Hackers have recently started stealing payment cards using Bluetooth beacons.
According to studies, the increase in cyber threats targeted at the energy sector has grown significantly over the past few years. Such attacks not only compromise endpoints but also smart metering infrastructure (SMIs).
In fact, recent research conducted by a team from University College London suggests that hackers could potentially use IoT devices deployed across the globe to remotely manipulate smart grids.
Role Of VPN In Cyber Security
The Internet is rapidly becoming more interconnected all around the world, making it easier than ever before for hackers to carry out cyberattacks.
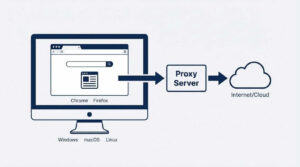
However, with the help of virtual private networks (VPNs), it becomes possible to prevent cybercriminals from accessing your computer network, thereby shielding your business from unwanted intrusions.
A VPN service provides protection against online threats such as viruses, Trojan horses, worms, spyware, keyloggers, botnets, denial-of-service attacks, distributed DoS, and phishing scams.
It encrypts your internet traffic while passing it through an encrypted tunnel. Encryption makes it harder for others to eavesdrop on your communications because they cannot read what you communicate.
While some companies and organizations choose to protect themselves by investing heavily in firewalls, antivirus software, intrusion detection systems, and various types of IDS, many do not.
The reason behind this is simple: most businesses can’t afford to hire enough experts in these areas to properly manage them. This is where Virtual Private Networks come in handy. All you need to do is subscribe to a reliable VPN and activate it whenever you are using the internet.
Final Words
There are a large number of cyberattacks on almost every online infrastructure. Since smart grids are IoT-based, therefore, they are vulnerable to such kinds of threats too! Therefore, it is best to provide security to such kinds of infrastructures.
Virtual private networks can be an excellent means of security for online networks. It encrypts the traffic coming in and going out, which helps prevent cyberattacks. We hope you find this article interesting and helpful.
Please let us know if you have anything in your mind related to smart grids and cyber security.







MAKECOMMENT