Table of Contents
Social Networking Sites are the Main Target of Phishing Sites
Social media has become an integral part of many people’s lives, and it’s only going to get more popular. As a result, threat actors are now abusing social media in the same way they started targeting mobile users. This threat has a specific name – phishing. Let us explain in detail what phishing is and why social media sites are the main target of phishing scams in the latest threats to your online presence.
Social Media and Phishing
Despite the fact that marketing departments are well-known for keeping tabs on social media in order to protect and promote their brands, they are unprepared to deal with the advances in social media that are becoming increasingly common. The tools typically used to monitor social media have issues similar to those that email security faces in the face of missing social engineering-based attacks.
A phishing scam is a type of social engineering that is carried out through the use of digital means. There are many types of phishing on social media, including:
- Impersonation
- Theft of credentials
- Proliferating threats
- Dumps of information
- Scams involving love and romance
- Scams totaling 419 (Nigerian prince)
- Gathering of intelligence (for account takeover and spear phishing)
We found a near 200 percent increase in social media abuse in 2018 and that number is only expected to rise. More than 5% of all social phishing attacks target users on social media sites. Only minimal controls are in place to prevent further account takeovers, and because social accounts typically need to be approved prior to connecting with people, they provide a greater sense of trust.
Read More: Facebook AI: What Privacy & Security Experts (and Everyday Users) Really Need to Know
It’s Bigger Than You’d Expect
An embedded tweet in a news story or an Instagram feed of cute puppies are all possibilities you may come across on any given day. However, the dangers to social media as a whole go far beyond the most popular sites. The social media ecosystem includes blogs, forums, news sites, paste and doc sites, and even gripe sites.
Consider, for example, your own company. You may already have established social media profiles for your brand, but what about your customers and employees? An increased risk of cyberattacks occurs when a digital medium becomes more widely used and popular. Security teams require strong social media protection solutions in order to be proactive in their defenses against these dangers. Amongst the downsides besides social phishing, phishing scams can also cause battery drains (especially for known iPhone battery drain).
How Social Media Is Abused
While we’ll go into more detail about how social media is being abused in the coming weeks, we’d like to start by expanding our understanding of what phishing is.
More TechInDeep News:
Infrastructures for C2 systems
While social phishing attacks are nothing new, short URLs are becoming more common on Twitter. A combination of Twitter’s URL shortened and other threat actors’ (and pentesters’) C2 infrastructure can be used to hide malicious links.
Impersonation
Impersonation is critical to a social phishing attack’s success because the tactic relies on social engineering to trick its victims. There are many ways in which you can damage a person’s reputation or brand by pretending to be an authority figure. Parody accounts aren’t included in this, but rather incidents that have a negative impact on users. It is not uncommon for threat actors to pretend to be a celebrity’s Twitter follower and reply with a message about a free bitcoin giveaway. The answer is no.
Theft and Dissemination of User Credentials
Users are tricked into entering their credentials into bogus landing pages by threat actors who not only conduct social phishing attacks directly on social media platforms. There are a number of ways in which a user’s account can be accessed by a threat actor, including a BEC attack in which they ask for a wire transfer.
Data Dumps
Dump files containing breached databases are not uncommonly circulated on the internet. Even on the dark web or in other marketplaces, this can happen. These data dumps can then be used in sinister ways by the highest bidder, or more.
Gathering of information
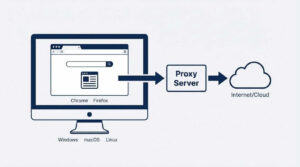
What was the name of your first animal companion, right now? Isn’t it a little fluffy? Fortunately, that post you posted on social media ten years ago contains the information we use to reset passwords. Do you want to share more personal details about your life? Threat actors, on the other hand, may be able to find this information and use it to craft a targeted spear phishing campaign. All these security hazards can be however mitigated by the use of Virtual Private Networks (VPN) like VeePN. To avoid such instances, you can easily download and install the Chrome free VPN on browsers in all your devices where you often access social media. In this case you will not only be cyber-protected, but you will also have access to Geo-restricted content.
Social media is supposed to be both entertaining and educational. Make sure it doesn’t get ruined by the crooks. Be aware that attackers may use one successful exploit to target not only you, but your family members, friends and coworkers as well as your boss.









MAKECOMMENT