
Determining whether the software running on your computer is genuine has become critical in 2025, as counterfeit and pirated software pose escalating security threats to both individuals and businesses. Software license verification is the process of confirming that installed programs are authentic, legally obtained, and unmodified from their original versions. With over 37% of software worldwide being unlicensed and counterfeit software containing malware in more than 80% of cases, understanding how to verify software authenticity protects users from security vulnerabilities, legal consequences, and financial losses.
The stakes are high: digital piracy costs the global technology industry approximately $75 billion annually, with projections reaching $125 billion by 2028. More importantly for end users, malware infections from counterfeit software can cost businesses up to $2.4 million per incident, with remediation taking an average of 243 days. This comprehensive guide explains software license verification methods, red flags for counterfeit software, and practical steps to ensure your programs are genuine and secure.
Table of Contents
Understanding Software License Types and Verification Requirements
Before diving into software license verification techniques, users must understand the three primary license types that dominate the market: OEM (Original Equipment Manufacturer), Retail, and Volume licenses. Each type has distinct characteristics affecting how software license verification is performed.
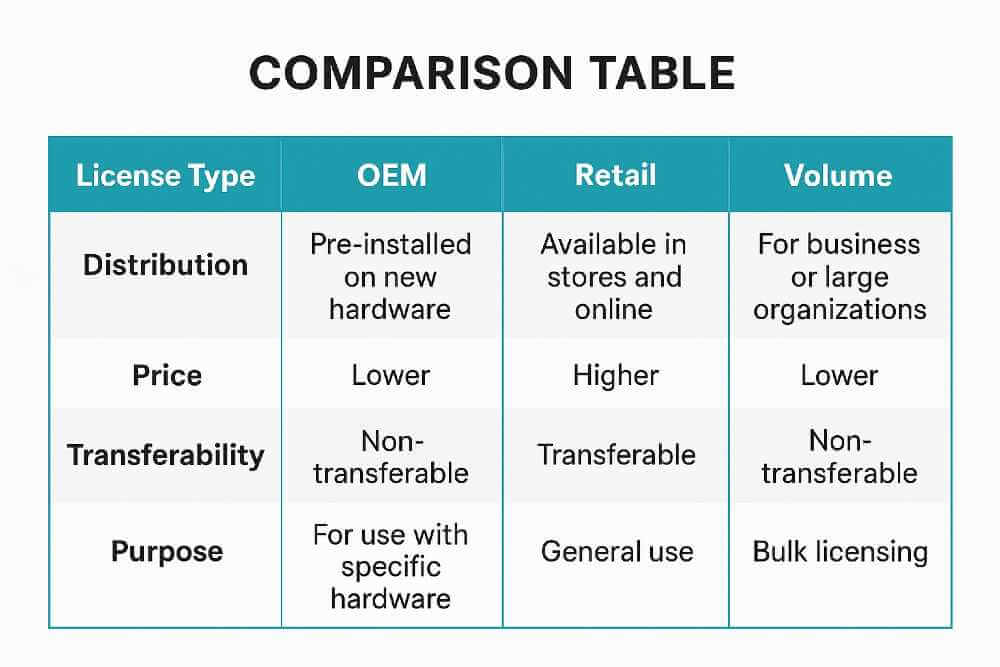
OEM licenses are pre-installed on new computers by manufacturers like Dell, HP, or Lenovo. These licenses are permanently bound to the original device and cannot be transferred to another computer. OEM versions typically cost less but lack direct manufacturer support and transferability. When verifying OEM software, users should look for the Certificate of Authenticity (COA) label physically attached to the device, which includes a holographic security feature and the product key.
Retail licenses are purchased individually from authorized retailers or directly from software publishers. Unlike OEM licenses, retail versions can be transferred between devices and are linked to the user rather than the hardware. Retail licenses come with complete manufacturer support and updates. Software license verification for retail versions involves checking the product key against the publisher’s validation servers and ensuring the license hasn’t been used on multiple devices simultaneously.
Volume licenses are designed for businesses and organizations requiring multiple installations. A single activation key authorizes software on numerous devices, making deployment more efficient. Volume licenses typically require organizational validation and are managed through centralized licensing platforms. Software license verification for volume licenses involves confirming the organization’s agreement with the software publisher and ensuring the number of active installations doesn’t exceed the purchased quantity.
Understanding the three main license types is essential, but equally important is knowing where to purchase genuine software to ensure you’re getting legitimate products. Purchasing from authorized vendors is the foundational principle of software license verification. Trusted platforms like Refortek specialize in providing 100% genuine software licenses—including Windows, Microsoft Office, and Adobe Creative Suite products—with instant activation, full technical support, and significant cost savings compared to retail pricing. Refortek’s commitment to authentic licensing, combined with their extensive inventory of verified products and secure payment processing, exemplifies the standards you should expect from any software vendor. By purchasing from authorized dealers who prioritize license authenticity and customer verification, users eliminate the risk of acquiring counterfeit software before installation, rather than attempting to verify potentially compromised programs after the fact.
Digital Signatures and Code Signing Certificates
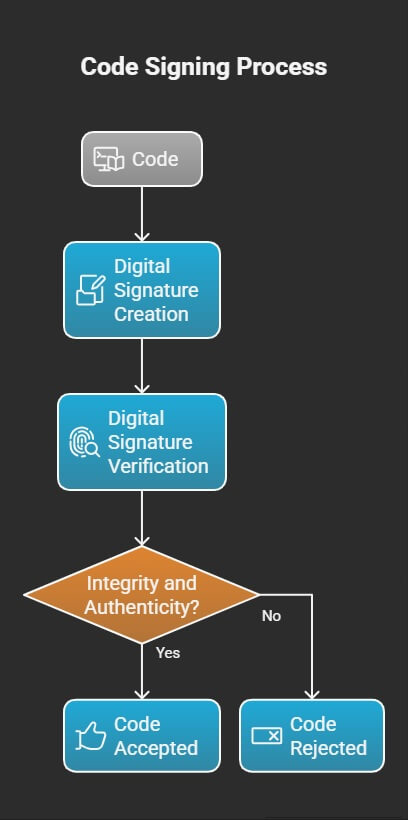
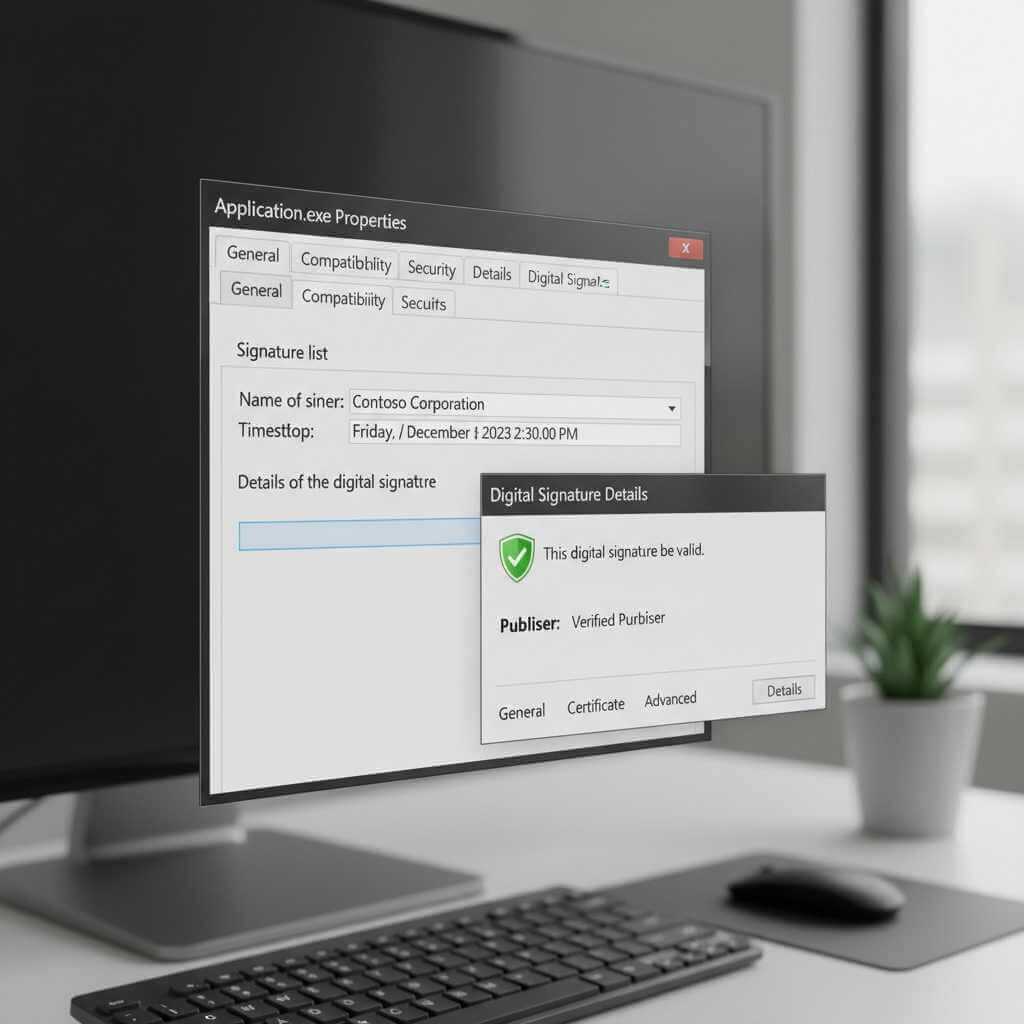
One of the most reliable methods for software license verification involves checking digital signatures and code signing certificates. A code signing certificate is a digital certificate that developers use to sign applications, drivers, and executables, proving the software’s authenticity and integrity.
When software publishers sign their programs, they create a cryptographic hash of the code and encrypt it with their private key. This digital signature is embedded within the software package along with a code signing certificate containing the publisher’s identity and public key. When users download or install the software, their operating system uses the certificate’s public key to verify the signature and confirm the code hasn’t been altered since signing.
Software license verification through digital signatures provides two critical assurances: authentication of the software publisher’s identity and confirmation that code hasn’t been tampered with after publication. Major operating systems like Windows and macOS automatically check digital signatures during installation, displaying security warnings when software lacks valid signatures or comes from unverified publishers.
To manually verify a digital signature on Windows, users can right-click the executable file, select Properties, navigate to the Digital Signatures tab, and examine the certificate details. The Subject field should display the legitimate company name matching the software publisher. Users can also use Microsoft’s SignTool utility from the Windows SDK to verify signatures via command line.
For enhanced software license verification, Extended Validation (EV) code signing certificates provide the highest level of publisher authentication. EV certificates require rigorous identity verification by certificate authorities and use hardware security modules to protect private keys. Software signed with EV certificates gains instant reputation with Windows SmartScreen Filter, eliminating security warnings for new users.
Verifying Software Through Hash Values and Checksums
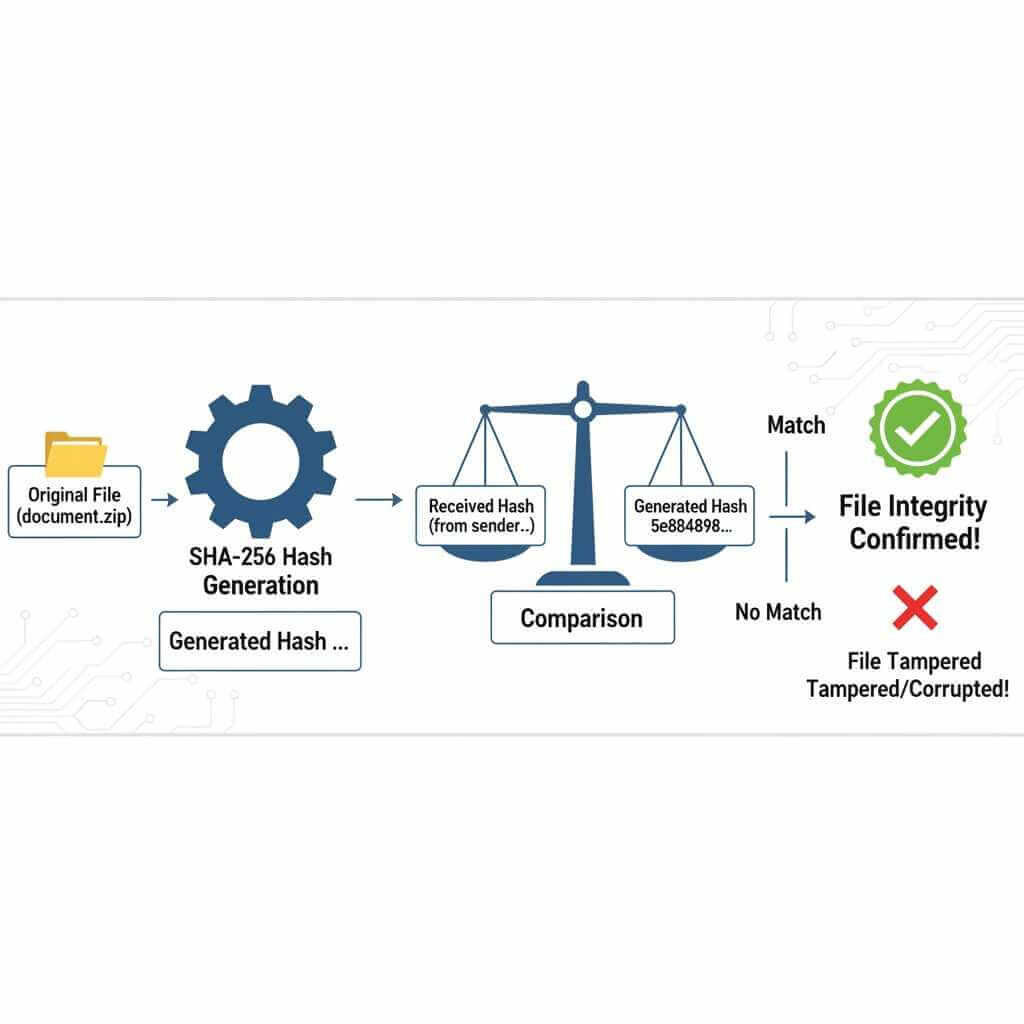
Software license verification also relies on cryptographic hash functions that create unique digital fingerprints for files. Publishers calculate hash values (typically MD5, SHA-1, or SHA-256) for their legitimate software and post these values on official websites. Users can then calculate hashes for downloaded files and compare them against official values to verify authenticity.
Hash verification confirms two important aspects of software license verification: that the downloaded file matches the publisher’s official version and that transmission hasn’t corrupted the file. Even a single byte modification produces a completely different hash value, making this method extremely effective for detecting tampering.
On Windows systems, users can verify hashes without additional software using the built-in certutil command. Opening Command Prompt and executing certutil -hashfile filename.exe SHA256 calculates the SHA-256 hash for the specified file. Comparing this output against the hash published on the official website confirms file authenticity.
Linux and macOS users have similar built-in tools. The sha256sum filename command on Linux and shasum -a 256 filename on macOS generate SHA-256 hashes for software license verification. Third-party tools like HashTools, MD5 & SHA Checksum Utility, and Download Hash Verifier provide graphical interfaces for users preferring visual hash comparison.
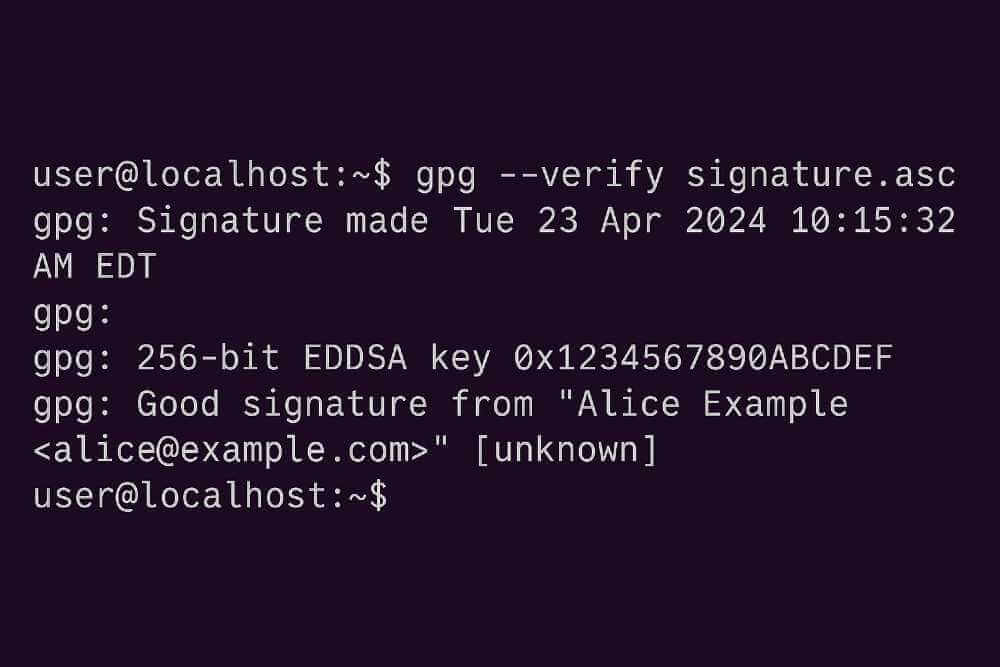
For comprehensive software license verification, users should always download hash values from official HTTPS-secured websites rather than third-party sources. Some software publishers also provide GPG signatures that offer additional verification through public key cryptography, combining hash verification with publisher authentication.
License Key Validation and Online Activation
Modern software license verification frequently involves license key validation through online activation systems. When users enter product keys during installation, the software contacts the publisher’s validation servers to confirm the key’s legitimacy, check for usage violations, and authorize the installation.
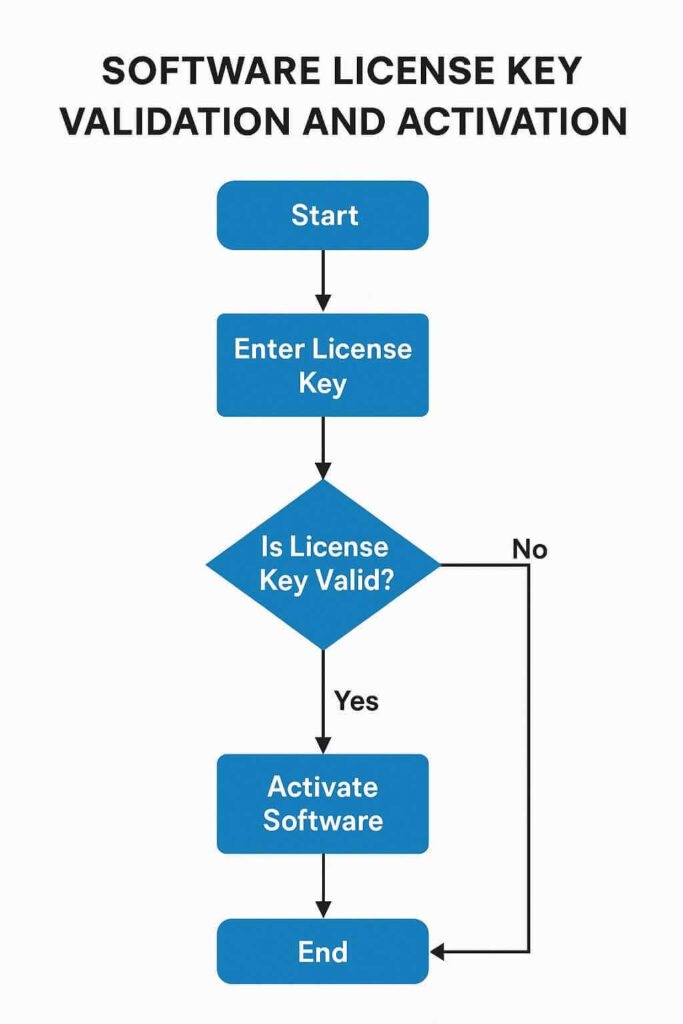
Online activation systems maintain databases of issued license keys, tracking which keys have been activated and on how many devices. This prevents counterfeit keys from working and detects when legitimate keys are being shared illegally across multiple installations. Software license verification through activation also enables publishers to revoke compromised keys and prevent their future use.
For Windows software license verification, users can check license status using the Software Licensing Management Tool (slmgr). Opening Command Prompt with administrator privileges and executing slmgr /dlv displays detailed license information, including the description channel (which should show “OEM” or “Retail” rather than “Volume” for consumer licenses) and activation status.
Alternative tools like ShowKeyPlus from the Microsoft Store provide graphical displays of Windows license information, making software license verification more accessible for non-technical users. The tool shows the license type, activation status, and whether the key is genuine.
Suspicious pricing often indicates counterfeit keys requiring enhanced software license verification. Software auditors typically assume that products sold for less than 90% of manufacturer’s suggested retail price (MSRP) are counterfeit or illegally transferred. Academic, home, or student versions sold for commercial use also represent license violations, even when the keys initially appear valid during activation.
Red Flags for Counterfeit and Pirated Software
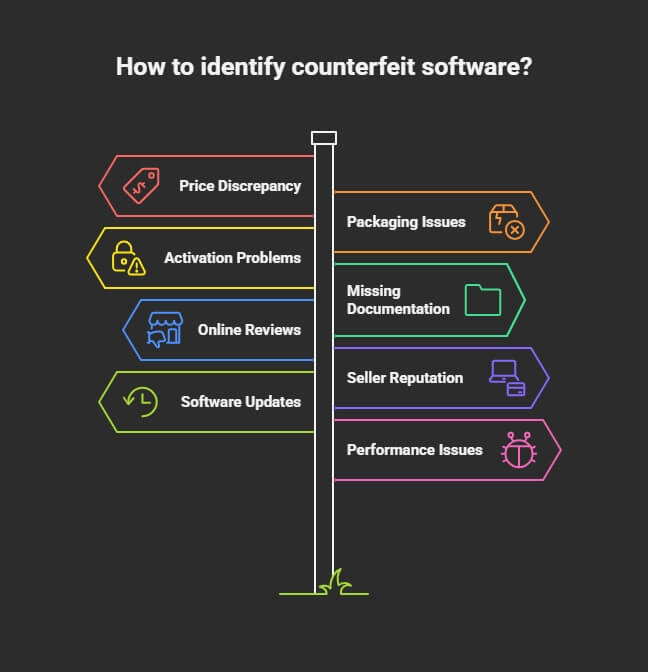
Recognizing warning signs helps users avoid situations requiring extensive software license verification after installation. Understanding these red flags prevents security risks before they materialize.
Excessive discounts represent the primary indicator of counterfeit software. While legitimate sales occur, discounts exceeding 10% of MSRP should trigger heightened scrutiny. Counterfeit software is often marketed with phrases like “genuine keys” or “legitimate serial numbers” despite being unauthorized or stolen.
Unclear source raises immediate concerns for software license verification. Downloading software from unofficial websites, peer-to-peer networks, torrent sites, or unknown vendors dramatically increases counterfeit risk. IDC research indicates that 78% of downloads from counterfeit software sources contain tracking cookies or spyware, while 36% include Trojans and malicious adware.
Missing security features signal potential counterfeit software. Legitimate programs include proper digital signatures, security certificates, and publisher information visible in file properties. Software lacking these elements or displaying “Unknown Publisher” warnings requires immediate software license verification.
Incomplete packaging or documentation often accompanies counterfeit physical media. Missing Certificates of Authenticity, poor-quality printing on disc labels, or absent holographic security features indicate counterfeit products. Official Microsoft software, for example, includes edge-to-edge holograms and distinctive security features.
License type mismatches represent common violations. Academic or home versions sold for commercial use, single-user licenses installed on multiple computers, and volume licenses used outside organizational agreements all constitute license violations requiring software license verification and remediation.
Unexpected behavior after installation suggests counterfeit or modified software. Programs requesting unusual permissions, installing unwanted toolbars or adware, displaying excessive advertisements, or failing to update properly may indicate compromised software requiring immediate software license verification and removal.
Platform-Specific Verification Methods
Different operating systems provide unique tools and methods for software license verification, tailored to their architectural requirements and security models.
Windows software license verification leverages several built-in utilities. The Windows Genuine Advantage validation process confirms that critical licensing files haven’t been damaged or removed and that the hardware profile matches the registered product key. Users can initiate validation through Windows Update or by running the genuine validation tool.
Microsoft’s How to Tell website provides detailed guidance for identifying genuine Windows software, including visual guides for recognizing legitimate Certificates of Authenticity and security features. The site also enables users to report suspected counterfeit software.
For software license verification on Windows applications, the System Information utility (msinfo32.exe) displays installed software and licensing details. Users can also examine the Programs and Features control panel to identify installation sources and verify publisher information.
macOS software license verification emphasizes App Store validation and Gatekeeper security. macOS automatically verifies digital signatures for applications downloaded from the App Store and checks developer certificates for software from identified developers. The system maintains a database of approved developers and revokes certificates for compromised accounts.
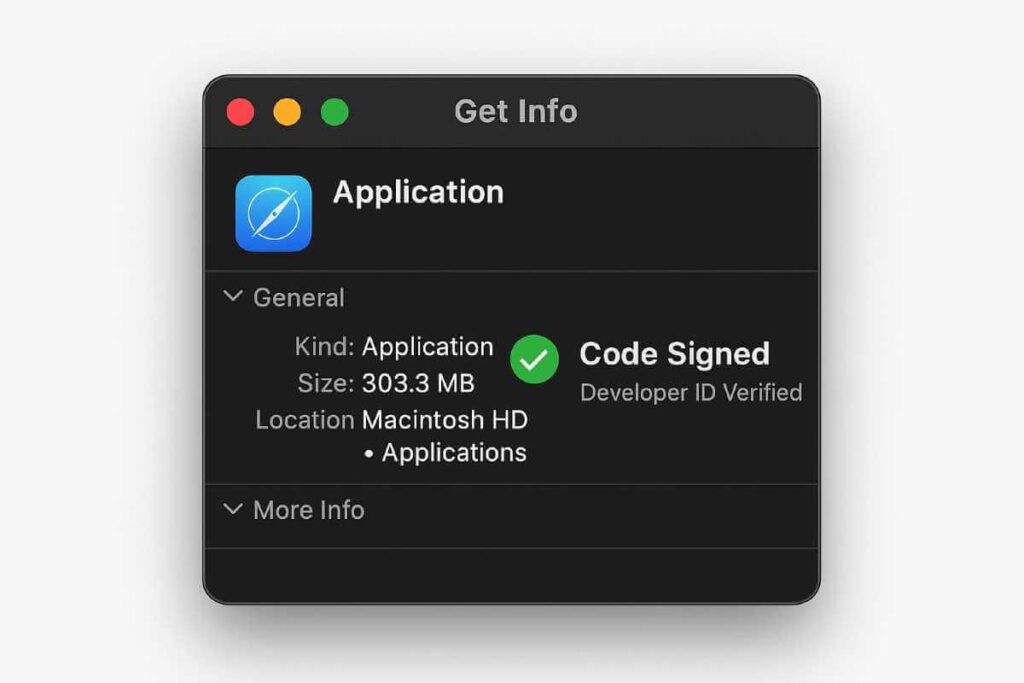
Users can verify macOS application signatures using Terminal commands. The codesign --verify --verbose command checks code signing status, while spctl --assess --verbose tests whether Gatekeeper will allow the application to run. These tools provide essential software license verification for macOS software obtained outside the App Store.
Linux software license verification typically involves package manager verification. Most Linux distributions use cryptographic signing for software repositories, automatically verifying package authenticity during installation. The gpg --verify command validates GPG signatures for manually downloaded software, confirming both source authenticity and file integrity.
Verifying Enterprise and Popular Software Licenses
Beyond operating system verification, users should apply additional scrutiny to commonly targeted software like Microsoft Office and Adobe Creative Suite, which represent significant investments and are frequent targets for counterfeiting.
For Microsoft Office licenses, users can verify authenticity through the “Help > Account” menu, where legitimate installations display license status, product key confirmation, and subscription details.
Adobe software provides similar verification through the “Help > Sign In” menu, displaying the user’s authentication status and confirming the software is tied to an authentic Adobe account. Organizations and individuals purchasing these high-value licenses from authorized providers like Refortek—which offers 100% genuine Microsoft and Adobe products with instant activation and technical support—gain the additional confidence that their software has undergone verification by the vendor before reaching customers.
This vendor-level verification, combined with personal post-purchase checks of digital signatures and license status, creates a comprehensive verification chain ensuring software authenticity from purchase through installation and ongoing use.
Protecting Against Malware in Counterfeit Software
The intersection of software license verification and cybersecurity cannot be overstated. Research consistently shows that counterfeit software serves as a primary malware distribution vector, with over 80% of pirated software containing malicious code.
Malware types commonly embedded in counterfeit software include keyloggers that record usernames and passwords, ransomware that encrypts files and demands payment, cryptocurrency miners that hijack system resources, spyware that monitors browsing and steals data, and backdoors that provide remote access to attackers.
The security consequences extend beyond individual systems. Network propagation allows malware from counterfeit software to spread across organizational networks, compromising multiple systems. Data breaches resulting from infected software can expose customer information, financial records, and intellectual property. Botnet recruitment turns compromised systems into attack platforms for distributed denial-of-service attacks.
Software license verification significantly reduces malware risk by ensuring software comes from verified publishers committed to security. Legitimate software receives regular security patches addressing newly discovered vulnerabilities, while counterfeit versions lack update mechanisms and leave systems exposed.
The financial impact of malware infections justifies rigorous software license verification procedures. Direct remediation costs average $10,000 per infected computer, while broader impacts include productivity losses during system downtime, legal liabilities from data breaches, reputational damage affecting customer trust, and regulatory fines for compliance violations.
Prevention strategies centered on software license verification include purchasing software exclusively from authorized vendors, verifying digital signatures before installation, maintaining current antivirus protection with real-time scanning, enabling automatic updates for operating systems and security software, implementing user access controls limiting installation privileges, and conducting regular security audits identifying unauthorized software.
License Compliance and Legal Considerations
Beyond security concerns, software license verification carries significant legal implications. Using unlicensed or counterfeit software violates copyright law and license agreements, exposing individuals and organizations to substantial penalties.
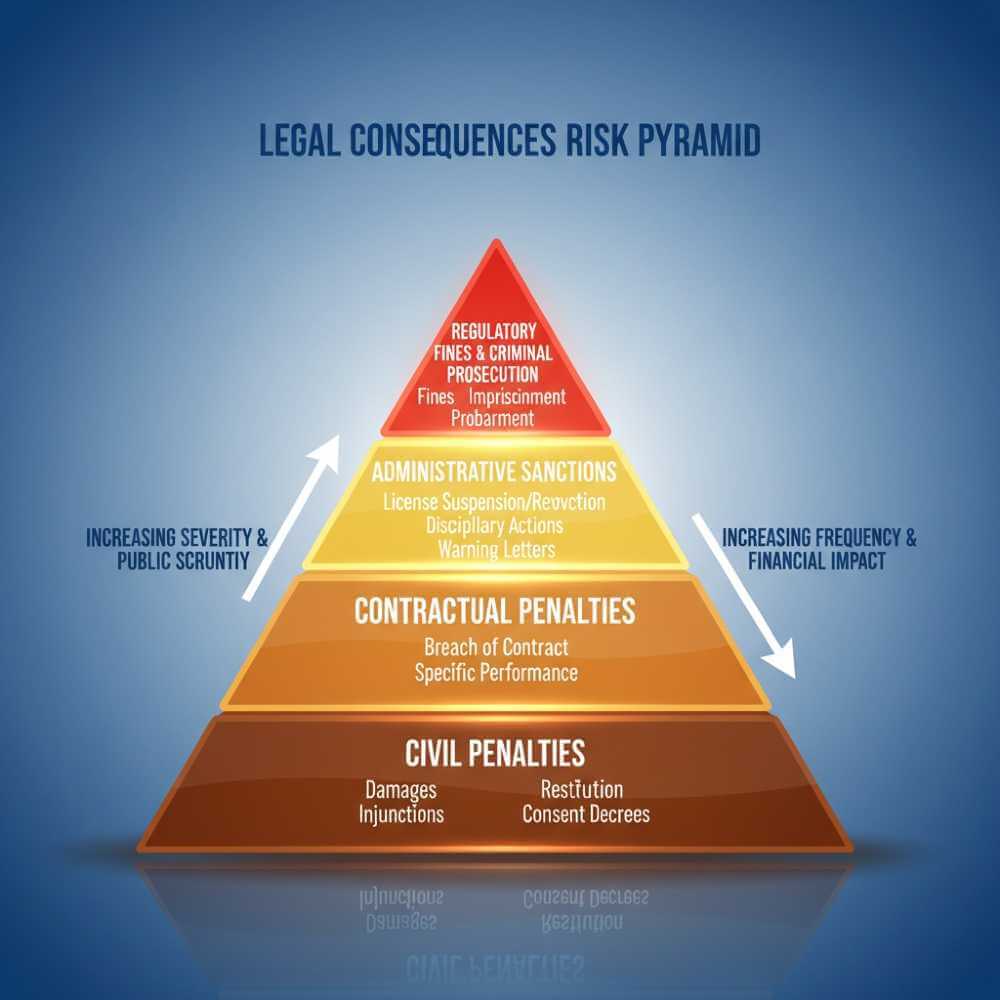
Legal penalties for license violations vary by jurisdiction but typically include civil fines ranging from hundreds to thousands of dollars per infringement, criminal charges potentially resulting in imprisonment for serious violations, and mandatory software audits forcing comprehensive software license verification across all systems. Organizations face particular scrutiny, with software vendors employing dedicated enforcement teams conducting surprise audits.
The audit process typically begins when vendors detect irregularities in usage patterns, organizational changes like mergers raising licensing questions, or reduced spending suggesting potential license violations. Organizations receiving audit notices should immediately form audit response teams, mark all audit communications as “Private and Confidential,” and engage legal counsel experienced in software licensing.
Compliance best practices minimize audit risks through comprehensive software license verification procedures. Organizations should maintain centralized license repositories documenting all software purchases, track installations ensuring usage doesn’t exceed entitlements, implement automated discovery tools identifying unauthorized software, conduct regular internal audits proactively addressing compliance gaps, and establish formal procurement processes requiring IT approval for software purchases.
Software asset management (SAM) tools automate software license verification by discovering installed applications, tracking license usage in real-time, monitoring compliance against agreements, alerting administrators to potential violations, and generating audit-ready reports demonstrating compliance status. According to experts from Refortek Adobe Partner and Microsoft Partner with extensive experience managing software environments in these ecosystems—leading SAM platforms integrate with procurement systems, help desk tools, and security infrastructure. Organizations working within Microsoft and Adobe software environments benefit particularly from solutions that understand the licensing complexities of these enterprise platforms, ensuring compliance across Office 365, Microsoft 365, Creative Cloud deployments, and related services.
Best Practices for Software License Verification
Implementing systematic software license verification procedures protects against security threats, legal risks, and financial waste. The following best practices establish comprehensive verification frameworks.
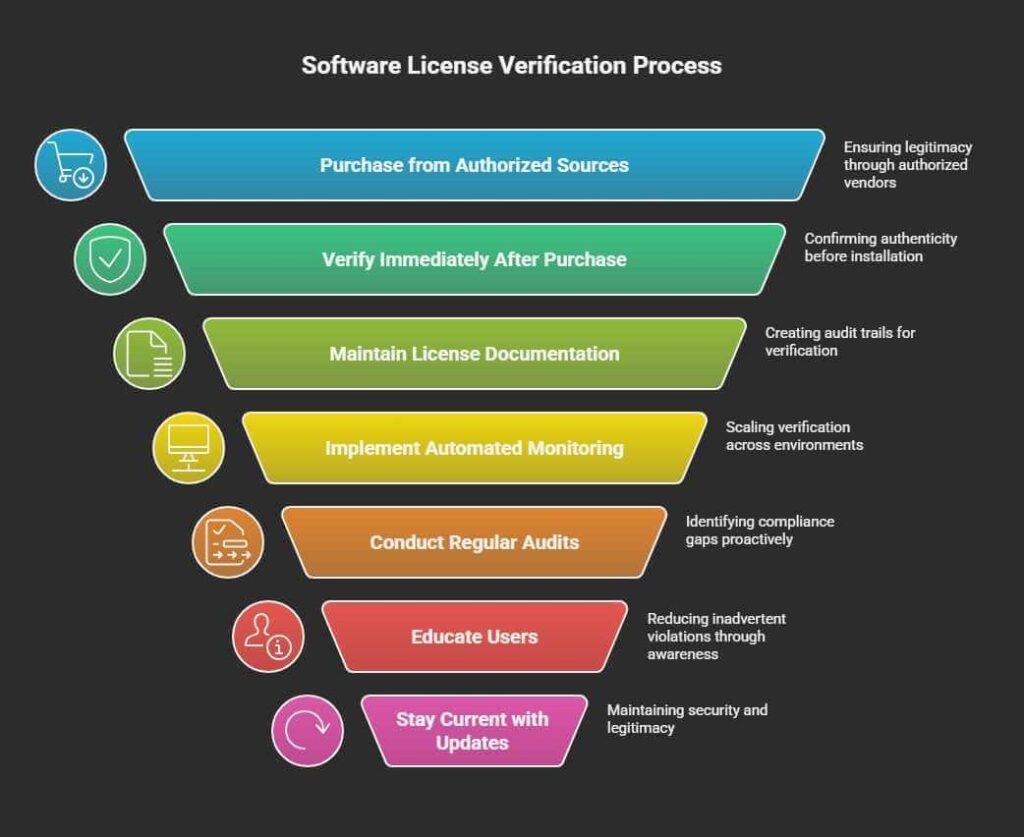
Purchase from authorized sources represents the foundational principle of software license verification. Buying directly from publishers, authorized resellers listed on official websites, or reputable retailers with verified partnerships ensures license legitimacy. Users should verify reseller authorization before purchasing, checking publisher websites for authorized vendor directories.
Verify immediately after purchase confirms license authenticity before installation. Check product packaging for security features, validate license keys through publisher websites or activation tools, examine digital signatures on downloaded software, and compare file hashes against official values. This immediate software license verification prevents installing compromised software.
Maintain license documentation creates audit trails supporting software license verification. Organizations should retain purchase orders and invoices, save license agreements and terms of use, document installation dates and locations, track renewal dates and maintenance agreements, and store authentication certificates and validation records. Centralized documentation repositories enable rapid verification during audits.
Implement automated monitoring scales software license verification across large environments. Automated discovery tools scan networks identifying all installed software, usage tracking monitors active licenses and detects excess installations, compliance checking compares usage against entitlements, and alert systems notify administrators of potential violations. Automation reduces manual effort while improving accuracy.
Conduct regular audits proactively identifies compliance gaps requiring software license verification and remediation. Organizations should schedule quarterly or semi-annual reviews, compare discovered software against authorized lists, verify that licenses match installations, identify redundant or unused licenses for reallocation, and remove unauthorized software. Regular audits demonstrate good faith efforts during vendor audits.
Educate users about software license verification reduces inadvertent violations. Training should cover organizational software policies, approved vendors and procurement processes, risks associated with unauthorized software, procedures for requesting new software, and methods for reporting suspicious programs. User awareness prevents shadow IT introducing unlicensed software.
Stay current with updates maintains security while supporting software license verification. Legitimate software receives regular security patches, feature updates, and bug fixes. Enabling automatic updates ensures systems remain protected, while update failures may indicate counterfeit software requiring verification.
Emerging Trends in Software License Verification
Software license verification continues evolving alongside technological advances and changing distribution models. Understanding emerging trends helps organizations prepare for future verification challenges.
AI-powered verification increasingly automates software license verification through machine learning algorithms analyzing software behavior patterns, identifying anomalies suggesting counterfeit software, and predicting compliance risks based on usage trends. These systems learn from vast datasets of legitimate and counterfeit software, improving detection accuracy over time.
Blockchain-based licensing creates immutable records supporting software license verification. Distributed ledgers track license purchases, transfers, and activations, preventing fraud while enabling transparent verification. Blockchain licensing platforms generate verifiable certificates confirming software authenticity without relying on centralized validation servers.
Continuous compliance monitoring shifts software license verification from periodic audits to real-time oversight. Cloud-based SAM platforms provide instant visibility into software usage, automatically comparing deployments against entitlements, alerting administrators to compliance drift, and generating compliance dashboards for management review.
Zero-trust architecture integration extends software license verification into comprehensive security frameworks. Zero-trust models require continuous verification of software authenticity, validate every application access attempt, integrate licensing verification with identity and access management, and dynamically adjust permissions based on verification results.
Software License Verification: FAQ
Q1: What is software license verification?
Software license verification is the process of confirming that installed programs are authentic, legally obtained, and unmodified from their original versions. It involves checking digital signatures, validating license keys, and verifying file integrity through hash values.
Q2: What are the three main software license types?
-
OEM – Pre-installed on new computers, permanently bound to hardware, no transfer allowed
-
Retail – Purchased individually, transferable between devices, includes full manufacturer support
-
Volume – Designed for organizations requiring multiple installations, managed through centralized platforms
Q3: How do I verify digital signatures on software?
-
Windows: Right-click file → Properties → Digital Signatures tab → Examine certificate details
-
macOS: Use Get Info window → Check Code Signed status and Developer ID
-
Linux: Use terminal commands like ‘codesign –verify’ or ‘gpg –verify’
Q4: What are the red flags for counterfeit software?
-
Excessive discounts exceeding 10% off MSRP
-
Unclear sources (torrents, unofficial websites)
-
Missing security features or publisher info
-
Poor packaging quality, missing Certificates of Authenticity
-
License type mismatches
-
Unexpected behavior (toolbars, ads)
-
Unusual permission requests
-
Failed update processes
Q5: What are the risks of using counterfeit software?
-
Malware: 80% of counterfeit software contains malicious code
-
Data Breaches: Cost $2.4M per incident on average
-
Legal Penalties: Civil fines to criminal charges with imprisonment
-
Compliance Violations: Mandatory audits and reviews
-
Remediation: 243 days average incident response
-
No Support: Loss of vendor support and patches
-
Network Risk: Malware spreads across systems
Q6: How do I verify hash values for software downloads?
-
Windows:
certutil -hashfile filename.exe SHA256 -
Linux:
sha256sum filename -
macOS:
shasum -a 256 filename
Compare generated hash against publisher’s official hash value. Exact match = authentic file.
Q7: What is code signing and why is it important?
Code signing uses a digital certificate to sign software, proving publisher identity and confirming code hasn’t been modified. Important because it:
-
Authenticates publisher identity
-
Confirms code integrity
-
Prevents malware distribution
-
Enables OS to verify legitimacy
-
Provides user confidence
-
Extended Validation (EV) certificates offer highest authentication level
Q8: What are the legal consequences of software piracy?
-
Civil fines ($100s-$1000s per infringement)
-
Criminal charges (potential imprisonment)
-
Mandatory software audits
-
Organizational compliance reviews
-
Regulatory fines per jurisdiction
-
Court-ordered remediation costs
-
Reputational damage
Conclusion
Software license verification has evolved from a simple administrative task into a critical security and compliance function. With 37% of global software unlicensed and over 80% of counterfeit programs containing malware, verification protects users from severe security risks, legal penalties, and financial losses.
Effective software license verification combines multiple approaches: checking digital signatures and code signing certificates, validating hashes against official values, confirming license keys through activation systems, recognizing red flags indicating counterfeit software, and implementing platform-specific verification methods. Organizations implementing comprehensive verification frameworks—including automated discovery, continuous monitoring, regular audits, and user education—minimize compliance risks while maximizing software investment value.
As software distribution continues shifting toward cloud services, subscription models, and digital marketplaces, software license verification methods will adapt accordingly. Emerging technologies like AI-powered detection, blockchain licensing, and zero-trust integration promise more automated and reliable verification. However, the fundamental principle remains constant: verifying software authenticity before installation protects against security threats while ensuring legal compliance.
Individuals and organizations prioritizing software license verification gain multiple benefits beyond avoiding counterfeit software. Legitimate programs receive security updates protecting against vulnerabilities, vendor support resolving technical issues, compatibility with other software and systems, and legal protection against infringement claims. The investment in proper verification procedures yields returns through enhanced security, reduced legal risk, and improved operational reliability.







